
The Blueprint for Resilience: Designing Your Enterprise Compliance Technology Architecture

THIS BLOG WAS WRITTEN BY THE COMPLIANCE & RISKS MARKETING TEAM TO INFORM AND ENGAGE. HOWEVER, COMPLEX REGULATORY QUESTIONS REQUIRE SPECIALIST KNOWLEDGE. TO GET ACCURATE, EXPERT ANSWERS, PLEASE CLICK “ASK AN EXPERT.”
You know that moment when the audit letter lands, or a new regulation drops, and a wave of dread washes over you? The scramble begins. Teams pull all-nighters, sifting through spreadsheets, emails, and disparate systems trying to piece together evidence. It’s inefficient, stressful, and honestly, it’s a massive risk. In today’s hyper-regulated world, relying on fragmented tools and reactive processes isn’t just unsustainable; it’s a liability.
What if your compliance function wasn’t a reactive cost center but a proactive, integrated system that actually strengthened your business? That’s not just wishful thinking; it’s the promise of a well-designed compliance technology architecture.
This isn’t just about buying another piece of software. It’s about strategically building an interconnected ecosystem of technologies that can absorb regulatory changes, automate monitoring, and provide real-time assurance. Think of it as constructing a robust, future-proof shield for your entire enterprise.
Table of Contents
- What is Compliance Technology Architecture?
- Beyond Point Solutions: Why Architecture Matters More Than Ever
- The Foundational Pillars of a Robust Compliance Ecosystem
- Deconstructing the Modern Compliance Technology Stack
- Strategic Architectural Patterns for Enterprise-Wide Compliance
- Critical Considerations for Designing Your Compliance Architecture
- Building Your Blueprint: A Phased Implementation Roadmap
- Overcoming the Roadblocks: Common Architectural Challenges
- The Future is Integrated: AI, Predictive Compliance, and Beyond
- Conclusion: Architecting a Proactive, Resilient Compliance Advantage
- FAQ: Your Compliance Architecture Questions Answered
- Sources
What is Compliance Technology Architecture?
Compliance technology architecture refers to the strategic framework and blueprint for designing, integrating, and managing all the technological components that enable an organization to meet its regulatory obligations. It encompasses everything from regulatory databases and workflow engines to API-driven ecosystems, ensuring a cohesive and efficient compliance program.
Beyond Point Solutions: Why Architecture Matters More Than Ever
The regulatory landscape is a living, breathing entity, constantly evolving. For businesses operating globally, this means juggling a dizzying array of frameworks – GDPR, HIPAA, SOC 2, ISO 27001, NIST, PCI DSS, SOX, and countless others specific to industry and region. This complexity isn’t just challenging; it’s expensive. IBM’s 2024 report pegged the global average cost of a data breach at $4.88 million. And honestly, that’s just one type of non-compliance.
Many organizations have responded by acquiring individual compliance tools: a system for risk management, another for policy documentation, maybe a third for audit management. But these often become fragmented point solutions, creating new silos and manual reconciliation nightmares.
This is where architecture comes in. It’s about designing a unified system that connects these tools, enabling a shift from periodic, reactive checks to continuous, proactive compliance. Hyperproof’s 2025 IT Risk and Compliance Benchmark Report found that companies using integrated and automated GRC tools were significantly less likely to experience data breaches (41%) compared to those managing risk reactively (60%).
The Foundational Pillars of a Robust Compliance Ecosystem
To build a strong compliance technology architecture, we first need to understand the fundamental activities that underpin any effective compliance program. Each pillar translates directly into a technological requirement.
- Written Policies & Procedures: Requires robust document management systems, version control, and automated distribution channels.
- Oversight: Needs comprehensive dashboards, reporting tools, and analytics for real-time visibility into compliance status.
- Training & Education: Implies learning management systems (LMS) integrated with attestation and tracking capabilities.
- Monitoring & Auditing: Demands continuous controls monitoring (CCM) systems, data aggregation, and anomaly detection.
- Internal Reporting & Issue Management: Calls for incident management, corrective action plans (CAP), and workflow engines.
- Enforcement & Discipline: Requires integration with HR systems and clear, trackable processes for disciplinary actions.
- Response & Remediation: Needs integrated incident response platforms, automated alerts, and forensic capabilities.
Deconstructing the Modern Compliance Technology Stack
A truly modern compliance ecosystem isn’t just a collection of software; it’s an integrated stack where each component plays a crucial role and communicates effectively with others.
Regulatory Intelligence and Horizon Scanning: Your Early Warning System
This is the eye on the horizon, constantly scanning for new and evolving regulations. An effective system in this area will consume, interpret, and disseminate regulatory updates in a structured, actionable format.
- API-driven Content Feeds: Rather than manually searching government websites, the architecture should integrate with specialized regulatory databases that provide real-time updates via APIs.
- Structured Data & Taxonomy: The intelligence shouldn’t just be raw text. It needs to be tagged, categorized, and linked to specific product types, regions, or business units.
- Expert Interpretation: Raw legislative text can be dense. A robust system often combines automated feeds with expert analysis to provide practical insights.
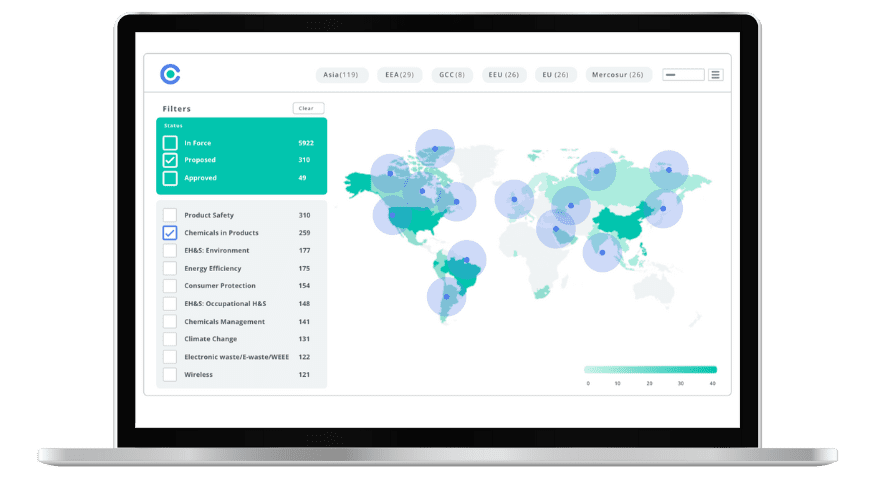
Platforms like C2P are designed precisely for this, tracking global regulatory requirements across 195 countries and housing over 110,000 global regulations.
Policy and Procedure Management: The Source of Truth
Your policies and procedures are the codified rules of your organization. Technologically, this means:
- Centralized Repository: A single source of truth for all policies, easily accessible and searchable.
- Version Control: Immutable tracking of all changes, approvals, and publication dates.
- Automated Distribution & Attestation: Ensuring the right policies reach the right employees and tracking their acknowledgement.
- Mapping to Regulations: Connecting specific policies to the regulations they address.
Risk and Control Assessment Engines: Automating the Core
This component moves beyond static risk registers to dynamic, automated assessment.
- Control Libraries: Mapping internal controls to multiple regulatory frameworks.
- Automated Assessments: Using questionnaires, data feeds, and even AI to continuously assess the effectiveness of controls.
- Risk Scoring & Prioritization: Quantifying risks and prioritizing mitigation efforts.
Evidence Collection and Audit Management: The Proof is in the Data
This is where the rubber meets the road – gathering the proof that your controls are working.
- Automated Evidence Gathering: Integrating directly with source systems to pull logs, configurations, user access reports, and other required evidence automatically. Automated evidence collection can reduce documentation time by 70%.
- Secure Audit Trails: Maintaining an immutable record of all collected evidence, making audit readiness a continuous state.
- Real-time Dashboards: Providing a consolidated view of compliance posture for internal stakeholders and auditors.
Workflow and Orchestration Layer: Connecting the Dots
This is the engine that drives your compliance processes. It uses business process management (BPM) tools and robotic process automation (RPA) to:
- Automate Compliance Workflows: Routing tasks, approvals, and escalations across departments.
- Integrate Siloed Systems: Ensuring that data and actions flow seamlessly between different compliance tools.
- Human-in-the-Loop Design: While automation is key, human expertise remains indispensable. Companies using automated regulatory tracking have reduced compliance-related delays by 50%.
Data Aggregation and Reporting: Actionable Insights
Imagine a single pane of glass for all your compliance data.
- Centralized Data Repositories: Consolidating data from all compliance components into a secure data lake or data warehouse.
- Advanced Analytics: Leveraging this aggregated data to identify trends and predict potential non-compliance.Customizable Reporting: Generating reports tailored for different stakeholders with relevant metrics and visualizations.
API-First Design for Interoperability: The Connective Tissue
This is perhaps the most critical architectural element that differentiates a truly integrated compliance ecosystem. An API-first approach means designing every component to expose its functionality through secure APIs.
- Standard APIs: Adhering to industry standards for APIs ensures easier integration.
- Common Data Formats: Defining consistent data models and taxonomies across systems prevents data translation headaches.
- Integration Patterns: Using established patterns to build a flexible compliance mesh rather than brittle point-to-point integrations.
- Security and Versioning: Treating APIs as first-class products, ensuring they are secure and backward-compatible. Professional services that offer API integrations can help automate compliance processes.
Strategic Architectural Patterns for Enterprise-Wide Compliance
Moving beyond individual components, let’s look at how these pieces fit together architecturally within an enterprise.
The Monolith vs. Microservices Dilemma
Traditionally, compliance software might have been a large, monolithic application.
- Monolithic Compliance: All functions are bundled into one large application. Pros: easier to manage initially. Cons: difficult to scale specific parts, slow to update.
- Microservices for Compliance: Breaking down compliance functions into smaller, independent services that communicate via APIs. Pros: greater agility, scalability, resilience. Cons: increased operational complexity.
For complex, global enterprises facing rapid regulatory change, a microservices-oriented approach often provides the necessary agility.
Cloud-Native Compliance Architectures
Leveraging public cloud platforms offers significant advantages for compliance. By July 2025, 56% of enterprises will have shifted to cloud environments.
- Scalability & Elasticity: Automatically scaling resources up or down to handle peak workloads.
- Cost-Effectiveness: Paying only for the resources consumed.
- Global Reach: Deploying compliance services closer to global operations.
- Managed Services: Utilizing cloud providers’ built-in security and logging services.
The C2P Platform is a cloud-based enterprise solution that exemplifies these advantages.
Hybrid Environments: Bridging Old and New
Many enterprises operate in hybrid environments, with a mix of SaaS platforms, on-premise legacy systems, and cloud applications.
- Vendor-Agnostic Integration: Focusing on open standards and APIs.
- Integration Middleware: Utilizing integration platforms to manage complex data flows between disparate systems.
- Data Synchronization Strategies: Implementing patterns to ensure data consistency across multiple systems.
Understanding how to effectively manage product compliance across diverse systems becomes critical.
Event-Driven Compliance: Real-Time Responsiveness
Imagine a system where every relevant action within your enterprise triggers a real-time assessment against your compliance controls.
- Event Producers: Operational systems publish events.
- Event Bus: A central messaging layer transports these events.
- Event Consumers: Compliance services subscribe to relevant events, perform automated checks, and generate alerts as needed.
This event-driven architecture supports continuous monitoring. 91% of companies plan to implement continuous compliance in the next five years.
Critical Considerations for Designing Your Compliance Architecture
When designing your compliance technology architecture, several key factors must be top of mind:
- Data Security & Privacy by Design: Security and privacy must be embedded into every layer of the architecture. Understanding data protection requirements is essential.
- Scalability & Performance: Design for future growth to handle increasing data volumes and regulations.
- Flexibility & Adaptability: The architecture should be modular and configurable enough to adapt quickly to new requirements.
- User Experience: Intuitive interfaces, clear dashboards, and streamlined workflows are critical.
- Leveraging AI & ML: AI can be integrated for predictive analytics, anomaly detection, and smart evidence correlation. 71% of respondents believe AI will have a net positive impact on compliance. Our coverage of artificial intelligence regulations helps organizations navigate this landscape.
- Human-in-the-Loop Design: Human expertise for interpretation and strategic oversight remains paramount. Organizations can leverage expert support to complement automated systems.
Building Your Blueprint: A Phased Implementation Roadmap
Designing and implementing a comprehensive compliance architecture is a strategic journey. Here’s a phased approach:
- Assess Current State: Document all existing compliance tools, processes, and data sources. Identify pain points.
- Define Future State & Requirements: Based on your challenges and goals, articulate your desired compliance posture.
- Select Technologies: Evaluate vendors based on their architectural requirements and integration capabilities.
- Design the Architecture: Create detailed architectural blueprints, including data models and integration patterns.
- Implement & Integrate: Begin with a pilot project. Iterate, learn, and expand.
- Monitor, Optimize & Iterate: Continuously monitor performance. Gather feedback and adapt to new requirements.
Organizations can benefit from professional services to ensure successful implementation.
Overcoming the Roadblocks: Common Architectural Challenges
Building a sophisticated compliance architecture comes with challenges:
- Legacy System Integration: Integrating older systems with modern platforms requires thoughtful planning.
- Data Siloing: Data can remain siloed if the architecture isn’t designed for seamless data flow.
- Vendor Lock-in: Over-reliance on a single vendor’s ecosystem can limit flexibility.
- Talent Gaps: Designing such an architecture requires a blend of compliance expertise and technical skills. Organizations can tap into a Knowledge Partner Network to supplement internal capabilities.
The Future is Integrated: AI, Predictive Compliance, and Beyond
The future of compliance architecture is undeniably integrated, intelligent, and proactive. We’ll see deeper adoption of AI for predictive analytics. Regulatory forecasting is emerging as the new standard, with AI-powered systems predicting regulatory changes months in advance.
Regardless of the specific technologies, the core principle remains: a strategically designed, integrated compliance architecture is the most powerful tool an enterprise has to navigate regulatory complexities.
Conclusion: Architecting a Proactive, Resilient Compliance Advantage
The era of disconnected compliance tools and reactive firefighting is over. Today’s global enterprises need a strategic, integrated approach to compliance technology architecture.
By focusing on a robust architecture that incorporates regulatory intelligence, sophisticated workflow, automated evidence collection, and an API-first design, you can transform your compliance function into a significant strategic advantage.
Compliance & Risks understands these challenges. With our flagship platform, C2P, and our team of over 40 subject matter experts, we provide the structured content, real-time alerts, and integrated tools necessary to help global businesses build and maintain a resilient compliance ecosystem.
FAQ: Your Compliance Architecture Questions Answered
- Q: What is the most important factor in compliance technology architecture?
Interoperability and an API-first design are arguably the most important factors. The ability for different compliance components to communicate seamlessly is crucial for automation and adaptability. - Q: How can I integrate legacy systems with new compliance tools?
Integrating legacy systems requires a strategic approach. This often involves using integration middleware, building custom API layers, or implementing data synchronization patterns. - Q: What role does AI play in compliance system design?
AI enhances compliance through predictive analytics, anomaly detection, and smart evidence correlation. Organizations can learn more about AI-powered compliance systems. - Q: How do I ensure scalability in my compliance architecture?
Design your architecture using principles like microservices, cloud-native deployments, and event-driven patterns. - Q: Why is an API-first approach critical?
An API-first approach ensures that all components can communicate effectively and flexibly, preventing vendor lock-in and enabling agility.
Sources
Additional Industry Reports and Standards:
- Ponemon Institute. (2024). Cost of a Data Breach Study 2024. Ponemon Institute LLC.
- Verizon Business. (2024). Data Breach Investigations Report 2024. Verizon Communications Inc.
- Gartner. (2024). Market Guide for IT GRC Technologies. Gartner, Inc.
- Forrester Research. (2024). The Forrester Wave™: Governance, Risk, and Compliance Platforms. Forrester Research, Inc.
- Cloud Security Alliance. (2024). Security Guidance for Critical Areas of Focus in Cloud Computing v5.0. CSA.
- Amazon Web Services. (2024). AWS Well-Architected Framework: Security Pillar. Amazon.com, Inc. Retrieved from https://aws.amazon.com/architecture/well-architected/
- Microsoft. (2024). Microsoft Azure Security Best Practices and Patterns. Microsoft Corporation.
- National Institute of Standards and Technology (NIST). (2024). NIST Cybersecurity Framework 2.0. U.S. Department of Commerce. Retrieved from https://www.nist.gov/cyberframework
- International Organization for Standardization. (2022). ISO/IEC 27001:2022 – Information Security Management Systems. ISO.
- European Union Agency for Cybersecurity (ENISA). (2024). ENISA Threat Landscape Report 2024. ENISA.
- Payment Card Industry Security Standards Council. (2024). PCI DSS v4.0 – Payment Card Industry Data Security Standard. PCI SSC.
- Deloitte. (2024). Tech Trends 2024: The Future of Enterprise Technology and Innovation. Deloitte Development LLC.
- McKinsey & Company. (2024). The State of AI in 2024: Generative AI’s Breakout Year and Enterprise Adoption. McKinsey & Company.
- Association of International Certified Professional Accountants (AICPA). (2023). SOC 2® Reporting on an Examination of Controls at a Service Organization Relevant to Security, Availability, Processing Integrity, Confidentiality, or Privacy. AICPA & CIMA.
- Institute of Internal Auditors (IIA). (2024). International Professional Practices Framework (IPPF) 2024 Edition. The Institute of Internal Auditors.
- OCEG. (2024). GRC Capability Model (Red Book) 4.0. Open Compliance and Ethics Group.
- ISACA. (2024). COBIT 2019 Framework: Governance and Management Objectives. Information Systems Audit and Control Association.
Experience the Future of ESG Compliance
The Compliance & Risks Sustainability Platform is available now with a 30-day free trial. Experience firsthand how AI-driven, human-verified intelligence transforms regulatory complexity into strategic clarity.
👉 Start your free trial today and see how your team can lead the future of ESG compliance.
The future of compliance is predictive, verifiable, and strategic. The only question is: Will you be leading it, or catching up to it?
Simplify Corporate Sustainability Compliance
Six months of research, done in 60 seconds. Cut through ESG chaos and act with clarity. Try C&R Sustainability Free.








